Code Protection: New MQL4 language(Build 600+) decompilation protection and other crack techniques.
From what Renat (CEO of Metaquotes) said :
- New ex4 are native code (like DLL) and no more pseudo code. So they are more difficult to decompile.
- ex4 are compressed (or other obfuscation technique not known) so have decompiled it's hard to understand it.
- ex4 for Market are encrypted. The exact technique used is not publicly available.
I report these information from memory, so I hope I don't make a mistake. Also I don't check these informations in practice.
Thank You for the answer but it didn't add much to my knowledge. Is it possible to decompile? might be possible in near future? (any bets?)
AFAIK, an encrypted product can't be decompiled. You have to decrypt it first. A product can always be decompiled. But it's a matter of costs. If it cost you 10$ to decompile an old ex4, maybe the new ex4 will need 1,000,000$ (just to say something). You got the idea ?
Hi,
I read about the new mql4(Build 600+) and already updated my EAs, now i have a question. How secure is the new protection against crackers and other types of executable cracking and modifying the code. EX: hex editing date of expiration, memory dumps, etc.. How secure is a simple time restriction(expiration date) on a EA now? How to implement new protection techniques using the new language?
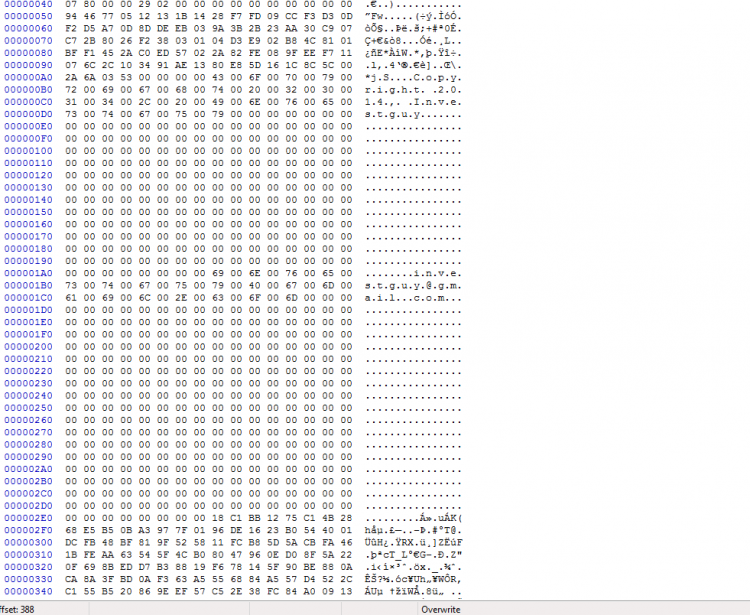
ex:
Thanks
AFAIK, there is not the possibility, until now, of a decompiler currently working for .ex4 compiled with Build 6xx
BUT, the problem with your code, for anyone really interested in cracking it, is that it is very easy to turn your
if (condition...) to
if (!condition
Or even easier, to NOP that return(1)
To resume, Decompiling is not possible now.
But what's still possible is dissassembling the code. And for anyone with little knowledge of assembler, reverse engeneering your code and cracking it would be fairly easy.
AFAIK, there is not the possibility, until now, of a decompiler currently working for .ex4 compiled with Build 6xx
BUT, the problem with your code, for anyone really interested in cracking it, is that it is very easy to turn your
to
Or even easier, to NOP that return(1)
To resume, Decompiling is not possible now.
But what's still possible is dissassembling the code. And for anyone with little knowledge of assembler, reverse engeneering your code and cracking it would be fairly easy.
- Free trading apps
- Over 8,000 signals for copying
- Economic news for exploring financial markets
You agree to website policy and terms of use
Hi,
I read about the new mql4(Build 600+) and already updated my EAs, now i have a question. How secure is the new protection against crackers and other types of executable cracking and modifying the code. EX: hex editing date of expiration, memory dumps, etc.. How secure is a simple time restriction(expiration date) on a EA now? How to implement new protection techniques using the new language?
ex:
Thanks